Protect Sensitive PII Data With Effective Log Management

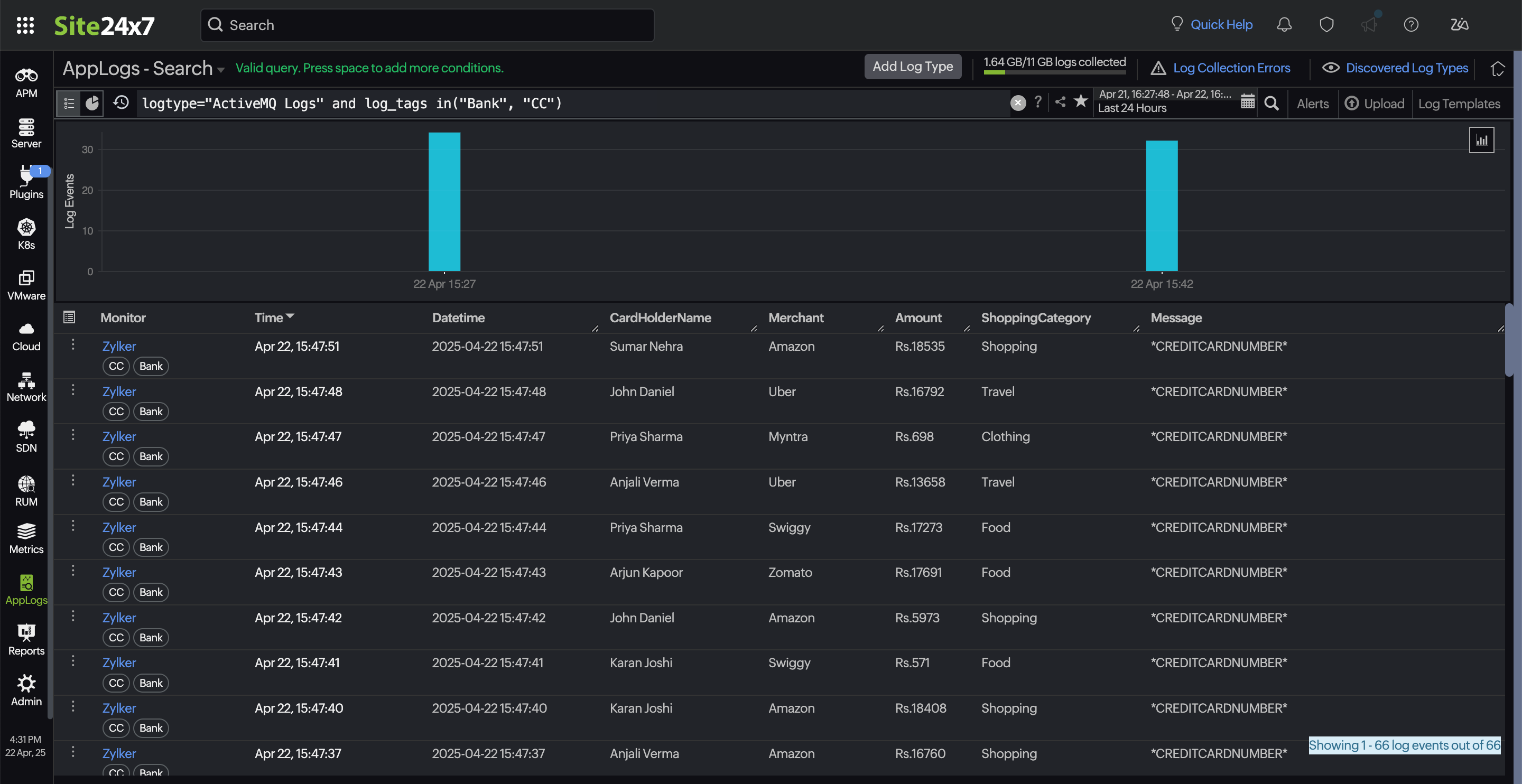
Organizations rely heavily on logs or tracking changes, troubleshooting issues, and addressing authentication attempts. Although these logs are essential for ensuring a smooth onboarding experience, they often contain users' personally identifiable information (PII), including names, email addresses, phone numbers, and sometimes location or device details.
The following sample log illustrates this scenario:
2025-11-01 09:12:33 [INFO] ACCOUNT_CREATED - New user registered: Name: Michael Scott, Email: zylker@zylker.com
While this log provides valuable insights for engineering and support teams, it also introduces significant data security and compliance risks if left unprotected.
This blog explains the impact of PII exposure in your logs and demonstrates how Site24x7’s log tagging can effectively mitigate this risk.
The growing risk of PII exposure in high-volume logs
When an organization processes thousands of logs containing PII each hour, manual restrictions and human review become impractical. As the log volume grows, so does the likelihood of sensitive fields being exposed in:
- Shared dashboards
- Developer or support troubleshooting sessions
- Automated reports
- Cross-team log access
- Compliance audits
Without effective control mechanisms, these logs become a liability, violating standards such as GDPR, CCPA, and ISO 27001, as well as internal data governance policies. This risk is especially high in environments where multiple teams share monitoring tools or inherit broad access permissions.
Proactive PII protection through log tagging
To mitigate PII exposure, organizations must adopt a proactive approach that both classifies sensitive information at the point of ingestion and protects it using automated security controls.
With PII-aware log tagging rules, teams can automatically detect patterns in user logs cultivated during onboarding, such as email formats, personal names, or keywords like ACCOUNT_CREATED, and assign appropriate tags that enforce secure handling.
These tags allow the system to automatically classify a log as sensitive and apply policies such as masking, hashing, or regex rules to conceal the data. Additionally, with Site24x7, PII data collected from the source are masked on the agent side before being transmitted as logs to the cloud. This ensures that logs containing PII are never exposed inappropriately, significantly reducing risk while maintaining operational visibility.
How Site24x7's log tagging can help mask PII data
- Detects email and name patterns automaticallyA log tag rule can be configured to search for predefined regex rules, such as:Log patternRegex ruleExplanationEmail ID[a-zA-Z0-9._%+-]+@[a-zA-Z0-9.-]+\.[a-zA-Z]{2,}Matches the username part of the email (letters, numbers, dots, underscores, %, +, -) and domain name and ensures that it ends with at least two characters.Name fieldsName:\s+[A-Za-z]+(?:\s+[A-Za-z]+)*,Matches the Name: field label and, one space after this field label, the first name and middle name, then ends with a comma to match the log format.ACCOUNT_CREATED\bACCOUNT_CREATED\b\b represents the word boundary and matches the string within it exactly.
You can organize the created log tags in a log tag group, allowing you to apply them to specific log types. Once identified, tags such as PII, Email, or Sensitive-Log can be automatically assigned, ensuring your logs are seamlessly categorized. - Applies masking and hashing at ingestionBefore transmitting the logs to the cloud, the tagging rules are applied to mask the PII data. For example, an email address will be masked and given a partially redacted name, such as z*****@zylker.com, ensuring compliance while preserving analytical usefulness.
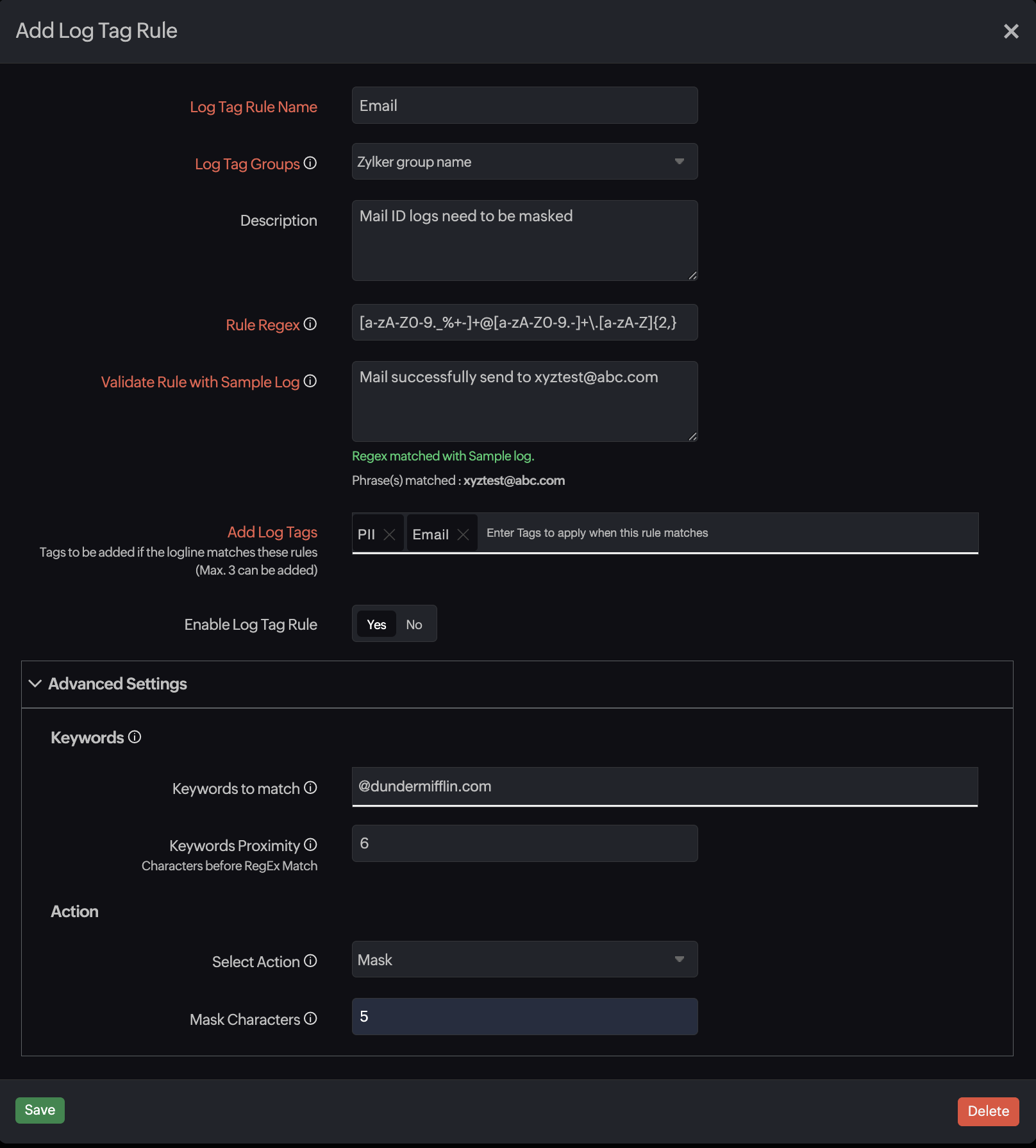
- Enables targeted alerts for unusual PII occurrenceIf PII appears in unexpected log categories or environments, you can set up a New Data Detection alert that can be triggered immediately for security teams.
Securing sensitive data at the log level
When sensitive PII data is exposed in logs, Site24x7’s log management solution automatically protects it through its log tagging feature.
By utilizing a regex rule, organizations can detect such data, mask or secure the log information, route it appropriately, and ensure compliance. This transforms a high-risk log stream into a controlled and secure component for an effective monitoring framework.
Topic Participants
Jenifer P